I Paid €1,329 for an iPhone and Discovered a Terrifying Secret War Happening Inside It.
Governments, hackers, and spyware companies are fighting for control of your phone right now - and Apple may lose.

My partner asked me last week why we are still paying €1,329 for an iPhone when Android flagships cost half that. I started explaining the security differences and realized something terrifying: most people have no idea there’s an invisible war happening inside their phones right now.
Apple’s security story isn’t just about Face ID and privacy labels; it’s about governments, spyware companies, and hackers fighting for control of the most personal device you own. And honestly? The battleground keeps getting more dystopian.
I will explain to you what we ignore and why you shouldn’t. Grab your morning coffee or tea, don’t stress or panic, because I want your full attention. Ignoring a single line in this article will cost you more than you think. Are you focused now? Ok, let’s start.
The Jailbreak Era: When iPhones Were Actually Yours
Remember the first iPhone? Of course, you don’t; you were probably still figuring out MySpace. But let me show you what really happened in 2007.
Steve Jobs unveiled this revolutionary device that couldn’t do basic shit. No wallpaper changes. No copy-paste. No App Store whatsoever, just the apps Apple decided you needed. People were simultaneously amazed and furious because Apple sold them this “everything device” that could barely do anything.
So naturally, hackers got to work.
A group calling themselves the “Dev Team” (with the most ridiculous pineapple logo) gathered some of the brightest minds in tech and did what seemed impossible: they broke through Apple’s restrictions. What they achieved is called privilege escalation, basically tricking the iPhone into thinking their code was authorized when it absolutely wasn’t.
Within months, passionate users published a 74-step process to jailbreak the first iPhone. It was crude, it was complicated, but it worked. And in March 2008, Cydia launched, a beautiful little app that became the holy grail for iPhone tinkerers.
Cydia lets you install “tweaks” that transform your locked-down iPhone into whatever you want. The biggest win? Carrier unlocking. The first iPhone only worked with AT&T, an American carrier with service so bad it became a national joke. George Hotz, a hacker who’d become legendary, unlocked this limitation in just 11 days using a soldering iron and insane precision.
But here’s the thing I keep thinking about: jailbreaking wasn’t just about aesthetics or convenience. It was about freedom from corporate control, from carrier monopolies, from anyone telling you what you could do with a device you bought with your own money.
That philosophical question still haunts me today.
Apple Fights Back (And Accidentally Makes iOS Incredible)
Apple obviously didn’t sit around watching hackers dismantle their carefully constructed ecosystem. They launched an all-out war, patching vulnerabilities with every update while hackers frantically searched for new exploits.
Different jailbreaks exploited different weaknesses. JailbreakMe used a PDF vulnerability; you’d visit a website, and boom, jailbroken. Evasi0n combined multiple bugs, including memory corruption issues. Pangu sent carefully timed commands to trick Apple’s security systems. Each method revealed another crack in Apple’s armor.
But this cat-and-mouse game had an unintended consequence: it made iOS exponentially more secure. Every vulnerability the jailbreak community exposed forced Apple to build better defenses. By 2009, viruses started appearing that specifically targeted jailbroken devices, stealing Apple IDs and iCloud accounts. The Wild West needed sheriffs.
Here’s what Apple built over the years, and why breaking into an iPhone now requires nation-state resources:
The Boot Process Fortress
When you turn on your iPhone and see that simple Apple logo, engineers see something completely different.
They see BootROM, the first code that executes when you power on the device, permanently etched into silicon. If BootROM gets compromised, everything built on top of it becomes vulnerable, and Apple can’t fix it with a software update.
They’d have to redesign the entire chip.
In 2019, an anonymous security researcher posted an exploit called “checkm8” on Twitter. Checkmate. Game over. It was a BootROM exploit affecting every iPhone produced before 2019, and it’s still there today because it’s physically impossible to patch.
After BootROM comes the Low-Level Bootloader (LLB), then iBoot, which verifies iOS authenticity, then the kernel, which controls everything: memory, software, network, battery. It’s the conductor of your phone’s orchestra, and compromising it means full control.
The Secure Enclave: Apple’s Vault Within a Vault
Your Face ID data and fingerprints are so sensitive that Apple doesn’t even store them with your other data. They live in the Secure Enclave, a completely separate hardware chip with its own operating system (called “Secure Enclave OS” or SEP OS). This chip handles encryption, stores your Apple Pay information, manages passwords, and never lets that data touch the primary system.
Every app on iOS exists in a “sandbox,” a secured container that can’t see what’s happening outside its walls. It’s isolation taken to an extreme level.
The article below is very interesting. The author was so underestimated.He explained everything in a very technical language only programmers or engineers would understand.
iOS Bootup Process and Jailbreaking
iOS Bootup Process and Jailbreaking iOS Bootup Process In Apple’s OS, the process of verifying the authenticity of…syed4asad4.medium.com
Over the years, every component became more isolated, making modifications nearly impossible. Jailbreaks became rarer, more complex, and less interesting to the average user. Apple started paying hackers millions through bug bounty programs, basically bribing them to report vulnerabilities instead of exploiting them.
And that’s when governments got involved.
Pegasus: When Your Phone Becomes a Spy
Here’s where this story gets really disturbing.
In 2010, NSO Group was founded in Israel by three veterans from Unit 8200, the Israeli army’s elite cyber warfare division. Their stated mission was to fight crime and terrorism. Their actual product was something far more powerful and terrifying.
They created Pegasus, spyware so sophisticated it’s classified as a military-grade weapon. Its sales are controlled by the Israeli Ministry of Defense. And Pegasus doesn’t work like normal malware that tricks you into clicking suspicious links.
Pegasus uses “zero-day” exploits, vulnerabilities that manufacturers don’t even know exist. Zero-day means Apple has zero days to fix the problem because they don’t know it’s there. The spyware remained secret until 2016, when an investigation revealed that at least 50,000 phone numbers worldwide had been targeted.
Journalists, activists, political leaders, and dissidents.
Modern versions of Pegasus can take complete control of certain devices without any action from the victim. These are called “zero-click attacks.” You don’t open a sketchy email. You don’t click a link. Also, you do absolutely nothing, and suddenly your phone is compromised.
Pegasus leaves almost no trace. It infects silently and siphons everything: messages, photos, location data, microphone access, camera access. One exploit called “ForcedEntry” infected phones by sending an SMS that the user never even had to open.
And Pegasus isn’t alone anymore. Companies like Grayshift and Cellebrite offer tools that extract data from iOS devices, though they typically require physical access and are less sophisticated. Still, the market for phone surveillance has exploded.
What keeps me up at night is this: these tools exist, governments use them, and Apple’s fighting a defensive war they might not win.
The San Bernardino Showdown: Privacy vs. National Security
A shooting in San Bernardino reported 14 dead and 22 injured on December 2, 2015. The FBI recovers the shooter’s iPhone 5C and immediately hits a wall: they can’t access the data.
iPhone encryption uses AES-256, a cipher with so many combinations that even supercomputers would take billions of years to crack. The FBI needs the passcode, but after 10 failed attempts, the iPhone automatically wipes all data.
So the FBI demands Apple create a special software tool to bypass these protections, essentially a primary key to unlock any iPhone.
Apple refuses.

If Apple gives the FBI this backdoor, what stops other governments from demanding the same access? What stops authoritarian regimes from forcing Apple to unlock dissidents’ phones? What happens to Apple’s entire brand promise of privacy protection?
The debate explodes across the internet. Media coverage intensifies. A fundamental question emerges: Does security require control, and if so, who should have that control?
Eventually, the FBI unlocks the phone without Apple’s help (they probably paid a private security firm millions to find an exploit). But this battle keeps repeating. The US, UK, Australia, and recently India have all pressured Apple to weaken encryption or provide backdoor access.
The China Compromise
Apple isn’t perfect, and they’ll bend when the stakes are high enough. Chinese iCloud accounts have their data stored in China, unlike the rest of the world. This is hugely controversial because Chinese law allows government access to that data.
Why did Apple agree? Because the Chinese market is massive, and because major manufacturing facilities (Foxconn, Pegatron) are in China. Though Apple’s now shifting production to India and Vietnam as geopolitical tensions escalate, showing they know exactly how precarious this balance is.
Privacy online basically doesn’t exist. While iCloud data is encrypted, metadata isn’t: contacts, emails, and usage patterns. You can tell apps not to track you, but that won’t stop them from collecting data, especially social media apps and most messaging services.
Apple imposes strict app restrictions not for user protection but to maintain control over its ecosystem. What really terrifies Apple is losing control of its devices.
Memory Integrity Enforcement: Apple’s Nuclear Option
In 2021, Apple sued NSO Group to ban Pegasus, with limited success. If the justice system can’t stop spyware companies, Apple has to engineer solutions itself.
Enter MIE: Memory Integrity Enforcement, the result of five years of research based on ARM’s Memory Tagging Extension (MTE) technology, heavily modified for iPhone hardware.
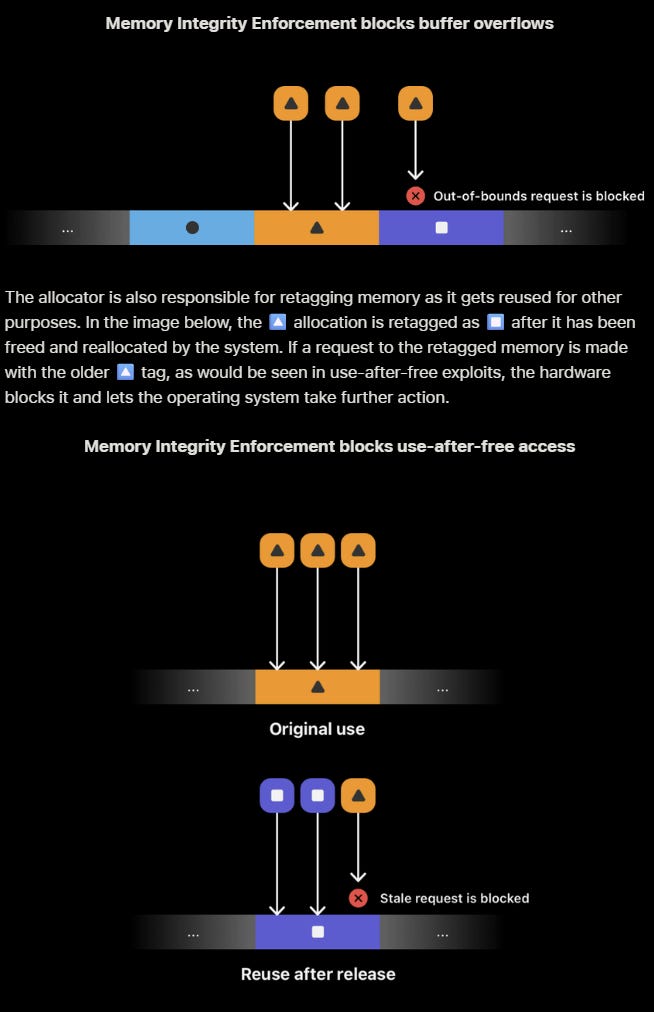
Here’s how it works: every memory allocation receives a secret tag, and the hardware verifies on every access that the tag matches. If spyware tries to access memory it doesn’t own, the system blocks it immediately.
This is being called one of the biggest security advances in years. It directly attacks how most spyware operates, exploiting memory corruption vulnerabilities to gain unauthorized access.
But we all know this won’t last. The battle will continue indefinitely.
The Uncomfortable Truth About Security
What started as a playground for passionate hackers seeking user freedom has become a battlefield involving governments, intelligence agencies, and billion-dollar surveillance companies.
On one side: early hackers fighting to expand user freedoms and device ownership rights.
In the middle: Apple, trying to balance protection with control, privacy with compliance, user rights with market access.
On the other side, governments and intelligence services demanding access to data for objectives that range from legitimate law enforcement to profound worry about authoritarian control.
This dilemma exists everywhere you look: each platform, every social network, every app. And it raises a question that honestly scares me more than any spyware:
Does security mean anything if it becomes the prison of what it claims to protect?
Final Thoughts
My partner still doesn’t understand why I pay €1,329 for an iPhone. After researching this article, I’m not entirely sure I do either. But I know one thing: the phone in your pocket isn’t just a device. It’s a battlefield where your privacy, your freedom, and your data are constantly under siege.
And most people don’t even realize a war is happening.
Please share your thoughts in the comments and stay tuned; plenty more to come on iOS 26, Apple’s ecosystem, and where the tech world is heading next. I wish you a happy New Year.






Pretty scary! Really makes you think…thanks!